Table of Contents
Introduction 🌿
In today’s digital age, protecting personal data is more important than ever. Privacy-Enhancing Technologies (PETs) are a set of innovative tools designed to safeguard individuals’ privacy while allowing them to interact freely online. These technologies aim to minimize the amount of personal data collected, protect the privacy of sensitive information, and give users more control over their digital footprint.
Think of PETs like a shield that helps guard your personal data from unwanted access. For example, when you use encrypted messaging apps like WhatsApp, the conversations you have are kept private—only you and the recipient can read them. This is an example of how Privacy-Enhancing Technologies work to ensure that even if your data is intercepted, it remains unreadable.
In a world where personal information is frequently shared and stored by various organizations, PETs are crucial in preventing misuse. Without these technologies, our data could be easily accessed, sold, or stolen. PETs not only protect privacy but also help build trust. Companies that implement PETs show customers that they care about their privacy, fostering a sense of security.
As digital surveillance, data breaches, and identity theft continue to rise, Privacy-Enhancing Technologies play a vital role in maintaining privacy rights. By using methods like encryption, anonymization, and secure data sharing, PETs provide users with the peace of mind that their personal data is protected. In short, Privacy-Enhancing Technologies are no longer a luxury; they are a necessity in today’s connected world, ensuring that privacy isn’t compromised as technology continues to evolve.
Why PETs Are Important
Today’s digital environment makes privacy protection along with data security crucial matters. We grant away our personal data without knowledge when we approve terms of service agreements repeatedly on websites and mobile applications. But this comes with risks. Technological developments have parallel developments in both data collection and its subsequent exploitation systems. The normal state of affairs today consists of extensive monitoring activities which governments together with corporations actively execute. Our activities through search engine use and shopping activities and social media interactions are consistently tracked by third parties who can use this information however they please.
The number of successful data security breaches keeps growing rapidly. Facebook and Target and Equifax together with other major companies have experienced data breaches which released sensitive information belonging to millions of users. Organizational control over consumer data has damaged the level of trust which people maintain during information sharing transactions.
The introduction of Privacy-Enhancing Technologies (PETs) creates ways to protect our data from unauthorized viewers. PETs implement encryption techniques together with anonymization and secure multi-party computation to give people the power of controlling their data through privacy preservation. Data privacy concerns in our digital era require Privacy-Enhancing Technologies (PETs) to become essential components in protecting user information.
What Are Privacy-Enhancing Technologies (PETs)? 🪪
PETs come in various forms, each serving a unique purpose. Encryption scrambles data so only authorized parties can read it. Anonymization removes personal identifiers, making it nearly impossible to trace data back to an individual. Secure Multi-Party Computation (SMPC) allows multiple parties to collaborate on data analysis without sharing the raw data itself. For instance, banks can detect fraud patterns without exposing customer details.
Common Features of PETs
What makes PETs stand out are their core principles. Data minimization ensures only the necessary data is collected—like a restaurant asking for your name but not your Social Security number. User control puts you in charge of your data, letting you decide who accesses it and how. Transparency means you’re always informed about how your data is being used, building trust.
In a world where data breaches are common, Privacy-Enhancing Technologies are becoming essential. They’re not just about protection—they’re about empowering users while enabling innovation. Whether it’s healthcare, finance, or AI, PETs are quietly reshaping how we handle data securely.
Types of PETs 🔏
Encryption
Encryption is one of the most widely used Privacy-Enhancing Technologies (PETs). It ensures that data is unreadable to unauthorized users.
End-to-End Encryption (E2EE)
This ensures that only the sender and receiver can read the data. For example, messaging apps like WhatsApp use E2EE to protect your chats.
Homomorphic Encryption
This allows computations to be performed on encrypted data without decrypting it. Imagine a bank analyzing your financial data without ever seeing it—this is what homomorphic encryption enables.
Anonymization Techniques
Anonymization removes or alters personal identifiers to protect individual privacy.
Data Masking: This hides specific data within a dataset. For instance, a company might mask customer names in a database to share it with analysts.
Pseudonymization: This replaces identifiable information with fake identifiers (pseudonyms). For example, a hospital might replace patient names with unique codes to share medical records for research.
Differential Privacy
Differential privacy adds “noise” to data to protect individual identities while still allowing useful analysis. Think of it like a survey where individual responses are hidden, but overall trends are visible. Companies like Apple use differential privacy to improve services without compromising user privacy.
Secure Multi-Party Computation (SMPC)
SMPC allows multiple parties to jointly compute a function over their inputs while keeping those inputs private. For example, two banks can compare fraud patterns without sharing sensitive customer data.
Federated Learning
Federated Learning enables AI models to be trained across multiple devices without transferring raw data. For instance, your smartphone can improve predictive text without sending your messages to a central server.
Zero-Knowledge Proofs
Zero-Knowledge Proofs allow one party to prove they know something without revealing the actual information. Imagine proving you’re over 18 without showing your ID—this is the power of zero-knowledge proofs.
Common Features of PETs
Data Minimization
PETs focus on collecting and processing only the data necessary for a specific purpose. For example, a weather app might only access your location when in use, rather than tracking you constantly.
User Control
PETs empower users to control their data. For instance, privacy settings in social media platforms let you decide who sees your posts.
Transparency
PETs ensure that data processing is transparent. Companies using PETs often provide clear explanations of how data is handled, building trust with users.
By combining these types and features, Privacy-Enhancing Technologies create a robust framework for protecting privacy in our increasingly digital world. Whether it’s encrypting your messages or anonymizing data for research, PETs are the silent guardians of your digital life.
How Privacy-Enhancing Technologies Work ⚙️
Privacy-Enhancing Technologies (PETs) are like the unsung heroes of the digital world. They work behind the scenes to protect your data while enabling innovation. Let’s break down how these technologies function, with real-world examples to make it relatable.
Encryption Techniques
Encryption is the backbone of data security. It scrambles your data into an unreadable format, ensuring only authorized parties can access it.
- How Encryption Protects Data: Imagine sending a secret letter in a locked box. Only the person with the key can open it. Encryption works similarly, safeguarding your data from hackers and unauthorized access.
- Types of Encryption:
- Symmetric Encryption: Uses the same key to encrypt and decrypt data. It’s fast but less secure if the key is compromised.
- Asymmetric Encryption: Uses a pair of keys (public and private). The public key encrypts data, and the private key decrypts it. It’s slower but more secure.
- Homomorphic Encryption: A game-changer! It allows computations on encrypted data without decrypting it. For example, a cloud service can analyze your encrypted health data without ever seeing it.
- Practical Examples:
- Messaging apps like WhatsApp use end-to-end encryption to secure your chats.
- Cloud storage solutions like Google Drive encrypt your files to protect them from breaches.
Anonymization and Pseudonymization
These techniques ensure data can’t be traced back to individuals, balancing usability and privacy.
- Anonymization: Removes all identifying information, making it impossible to trace data back to a person. For example, a hospital might share anonymized patient data for research without revealing identities.
- Pseudonymization: Replaces identifiers with fake ones (pseudonyms). It’s reversible with the right key. For instance, a marketing firm might pseudonymize customer data to analyze trends without exposing personal details.
- Use-Cases:
- Healthcare: Sharing anonymized patient data for medical research.
- Finance: Analyzing pseudonymized transaction data to detect fraud.
- Marketing: Tracking user behavior without compromising privacy.
Differential Privacy
Differential privacy adds “noise” to data, making it hard to identify individuals while preserving overall trends.
- Simplified Explanation: Think of it as a crowded room where everyone whispers. You can hear the general conversation but can’t pick out individual voices.
- Real-World Applications:
- Census Data: Governments use differential privacy to release population statistics without exposing individual details.
- Tech Companies: Apple uses it to analyze user behavior in iOS without tracking specific users. Google applies it in Chrome to study browsing patterns anonymously.
Secure Multi-Party Computation (SMPC)
SMPC allows multiple parties to collaborate on data analysis without sharing raw data.
- How It Works: Imagine three chefs creating a recipe together without revealing their secret ingredients. SMPC enables similar collaboration in data analysis.
- Industries Adopting SMPC:
- Financial Services: Banks use SMPC to detect money laundering without sharing customer data.
- Healthcare: Researchers collaborate on drug development without exposing patient records.
Federated Learning
Federated learning trains machine learning models across multiple devices without centralizing data.
- Overview: Instead of sending data to a central server, the model travels to the data. For example, your smartphone trains a model locally, and only the updates are shared.
- Privacy Benefits:
- Your data never leaves your device, reducing the risk of breaches.
- It’s a win-win for privacy and innovation, used by companies like Google for predictive text and Apple for Siri.
Zero-Knowledge Proofs
Zero-knowledge proofs let you prove something is true without revealing the underlying information.
- Simplified Use-Case: Imagine proving you’re over 18 without showing your ID. Zero-knowledge proofs work similarly, verifying facts without exposing sensitive data.
- Benefits:
- Verification Without Exposure: Used in blockchain for private transactions.
- Enhanced Privacy: Ideal for identity verification, voting systems, and financial transactions.
By understanding how these technologies work, you can see why PETs are essential in today’s data-driven world. They’re not just tools—they’re the foundation of trust in the digital age.
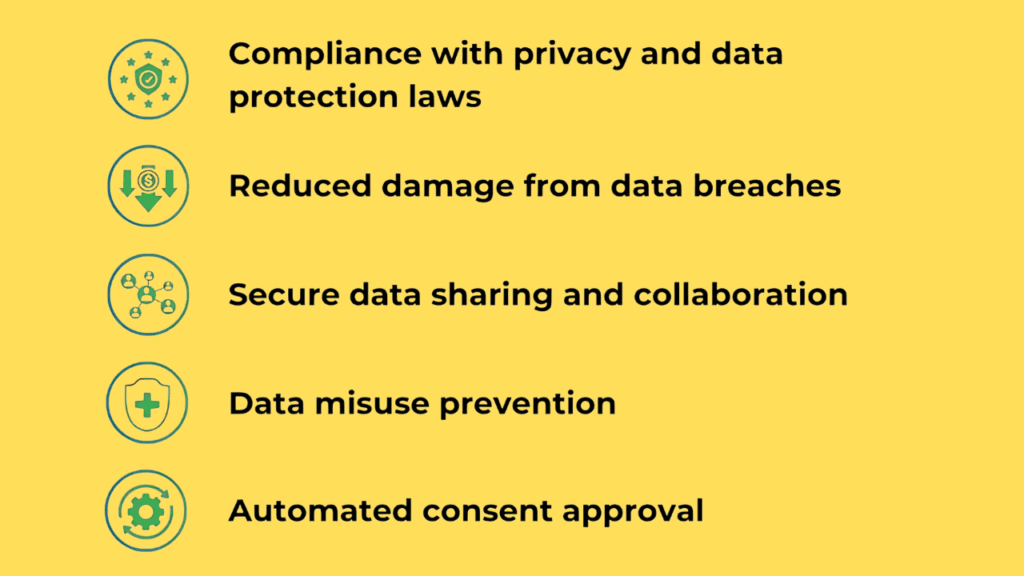
Importance and Benefits of Privacy-Enhancing Technologies 🌻
Privacy-Enhancing Technologies (PETs) are no longer just a nice-to-have—they’re a necessity in today’s data-driven world. From protecting sensitive information to building trust with users, PETs offer a wide range of benefits that can transform how businesses operate. Let’s dive into why PETs matter and how they can make a real difference.
Protection Against Data Breaches
Data breaches are a growing threat, with cyberattacks becoming more sophisticated every year. PETs act as a powerful shield, minimizing the risk of sensitive data falling into the wrong hands.
For example, technologies like homomorphic encryption allow data to be processed while still encrypted, meaning even if hackers intercept it, they can’t decipher it. Similarly, differential privacy adds noise to datasets, making it nearly impossible to identify individual users.
Take the 2021 Facebook data leak, where personal information of over 500 million users was exposed. Had PETs like anonymization been implemented, the impact could have been significantly reduced. By adopting Privacy-Enhancing Technologies, businesses can proactively protect their data and avoid costly breaches.
Regulatory Compliance and Legal Benefits
With regulations like GDPR (General Data Protection Regulation) and CCPA (California Consumer Privacy Act) in place, businesses are under increasing pressure to protect user data. Non-compliance can lead to hefty fines and legal consequences.
Privacy-Enhancing Technologies play a crucial role in helping businesses meet these regulatory requirements. For instance, data minimization—a core principle of PETs—ensures that only the necessary data is collected, reducing the risk of non-compliance. Additionally, secure multi-party computation (SMPC) enables businesses to share data for analysis without violating privacy laws.
A great example is how healthcare providers use Privacy-Enhancing Technologies to share patient data for research while staying compliant with HIPAA regulations. By integrating PETs, businesses can not only avoid penalties but also build a reputation for being privacy-conscious.
Enhancing User Trust
In an era where data privacy concerns are at an all-time high, user trust is more valuable than ever. PETs can be a game-changer in building and maintaining that trust.
When users know their data is protected by advanced technologies like end-to-end encryption or zero-knowledge proofs, they’re more likely to engage with a brand. For instance, messaging apps like Signal have gained massive popularity because of their commitment to privacy through PETs.
This trust translates into stronger customer loyalty and a better brand reputation. A study by Cisco found that 84% of consumers care about privacy, and 80% are willing to act to protect it. By implementing PETs, businesses can show users they take privacy seriously, fostering long-term relationships.
Competitive Advantage
In a crowded market, standing out is key. Early adoption of PETs can give businesses a significant edge over competitors.
Companies that prioritize privacy are seen as innovators and leaders. For example, Apple has differentiated itself by integrating PETs like differential privacy into its products, earning praise for its commitment to user privacy.
Moreover, PETs can open up new opportunities for collaboration. Businesses that can securely share data with partners or clients are more likely to form strategic alliances. For instance, financial institutions using PETs can collaborate on fraud detection without exposing sensitive customer data.
By embracing PETs early, businesses not only future-proof their operations but also position themselves as forward-thinking leaders in their industry.
Challenges and Limitations of Privacy-Enhancing Technologies ⚠️
Privacy-Enhancing Technologies (PETs) are transforming how we protect data, but they’re not without their challenges. Let’s explore the hurdles businesses face when adopting PETs and how they can navigate these obstacles.
Technical Complexity and Implementation Costs
Adopting Privacy-Enhancing Technologies often requires significant technical expertise and resources. Technologies like homomorphic encryption or secure multi-party computation are complex, and implementing them can be costly. For example, a healthcare provider wanting to use differential privacy for patient data might need to hire specialized staff and upgrade their systems—a hefty investment, especially for smaller organizations.
To overcome this, businesses can start small by piloting PETs in less critical areas. Cloud-based PET solutions can also reduce infrastructure costs, and partnering with experts can streamline the implementation process.
Performance Trade-offs
One of the biggest challenges with Privacy-Enhancing Technologies is balancing privacy with performance. Homomorphic encryption, for instance, allows computations on encrypted data but can slow down processing speeds. For a financial institution processing thousands of transactions in real-time, such delays could frustrate customers and hurt operations.
Similarly, differential privacy adds “noise” to datasets to protect individual identities, but too much noise can reduce the accuracy of data analysis. To address this, businesses can optimize algorithms, use hybrid approaches combining PETs with traditional methods, or invest in hardware acceleration to speed up computations.
Awareness and Education
A lack of awareness about PETs is another barrier. Many businesses and users don’t fully understand what PETs are or how they can benefit from them. For example, a marketing team might not realize that differential privacy can help analyze customer data without compromising individual privacy.
Education is crucial. Industry leaders, governments, and tech companies need to collaborate to raise awareness. Workshops, webinars, and case studies can help demystify PETs and showcase their value. Businesses can also train their teams, share success stories, and partner with academic institutions to promote research and education on Privacy-Enhancing Technologies.
Future Trends and Developments in PETs 🌱
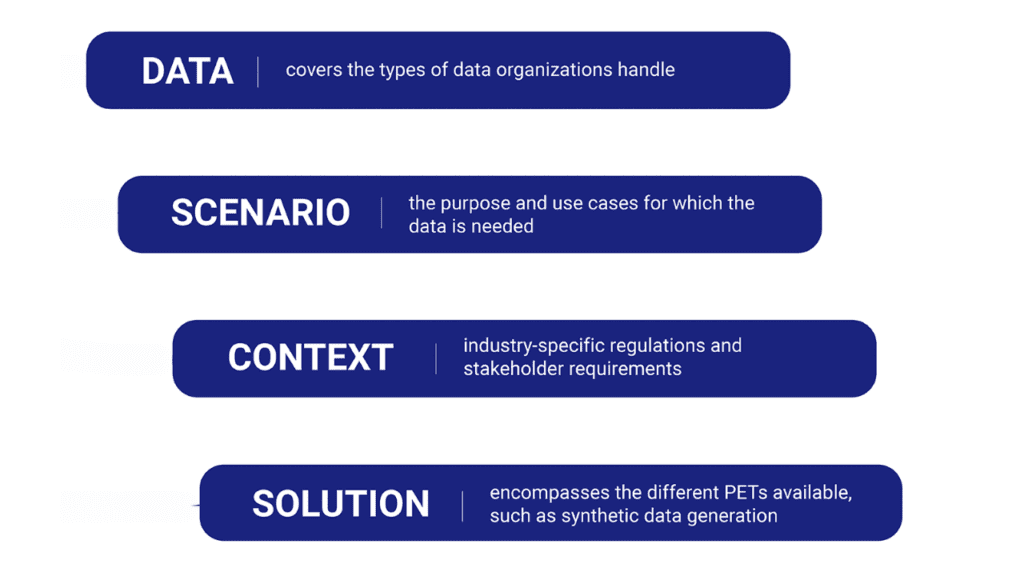
Emerging Technologies and Innovations in PETs
Privacy-Enhancing Technologies (PETs) are rapidly developing in the modern world and designers create innovative solutions which strengthen data protection while making them available to more people. Homomorphic encryption continues to improve its ability to execute faster data operations on encrypted files at the same time as researchers enhance the practical implementation of differential privacy through better utility versus privacy tradeoffs.
The recent advancement includes merging PETs with blockchain technology so users can share data in a decentralized manner while maintaining secure protection. PETs exist beyond theory because Apple and Google among others implemented them for protecting user data while providing personalized services.
Future Outlook: How PETs Might Shape Digital Privacy
Privacy-Enhancing Technologies (PETs) will emerge as essential standards for digital privacy protection due to increasing data breaches and privacy challenges. The future will allow users to maintain protected personal data throughout platform-wide sharing. The data protection provided by PETs guarantees complete encryption along with anonymization during all phases of information transfer.
PETs will become a standard practice within governmental bodies and organizations to meet the requirements of mounting privacy regulations including GDPR and CCPA. The shift towards data privacy empowerment lets individuals become managers of their personal data which will build trust throughout digital spaces.
Role of PETs in AI and Machine Learning Advancements
The development of AI together with machine learning makes substantial progress through the implementation of PETs. Privacy enhancement occurs through data segmentation techniques which consequently enables the use of broader datasets for precise artificial intelligence system performance. Privacy-Enhancing Technologies will ensure the win-win relationship between business innovation and user privacy protection as AI progresses forward.
Conclusion 🎯
Privacy-Enhancing Technologies (PETs) are no longer just a niche concept—they’re a necessity in today’s data-driven world. From homomorphic encryption to differential privacy, PETs offer innovative ways to protect sensitive information while enabling secure collaboration. As data breaches and privacy concerns continue to rise, adopting Privacy-Enhancing Technologies can help organizations stay compliant with regulations like GDPR and build trust with their users.
For individuals, Privacy-Enhancing Technologies provide peace of mind, knowing their personal data is safeguarded. For businesses, they unlock opportunities to innovate without compromising security. Whether you’re a tech enthusiast or a business leader, now is the time to explore and embrace PETs. After all, in a world where data is gold, protecting it is non-negotiable.
Let’s take the first step toward a safer digital future—together.
FAQs 💡
What are the most commonly used Privacy-Enhancing Technologies?
Common PETs include homomorphic encryption (processing encrypted data), differential privacy (adding noise to data), secure multi-party computation (collaborative analysis without sharing raw data), and zero-knowledge proofs (proving knowledge without revealing details). For example, Apple uses differential privacy to analyze user behavior securely.
Can PETs completely guarantee privacy?
PETs significantly enhance privacy but can’t guarantee it 100%. For instance, differential privacy reduces re-identification risks but isn’t foolproof. Combining PETs with strong security practices, like encryption and access controls, creates a more robust privacy framework.
How expensive is it for businesses to implement PETs?
Costs vary by business size and PET type. Small businesses may use affordable open-source tools, while enterprises might invest in advanced solutions like homomorphic encryption. However, the cost of not using PETs—like GDPR fines or data breaches—can be far higher.
What industries benefit most from adopting PETs?
Industries like healthcare (secure patient data sharing), finance (fraud detection without exposing customer data), and AI (training models on sensitive data) benefit greatly. For example, Google uses Federated Learning to improve AI without accessing raw user data.
How do PETs help companies comply with privacy regulations?
PETs help comply with GDPR, CCPA, and HIPAA by enabling data minimization, anonymization, and secure data sharing. For instance, a marketing firm can analyze trends without accessing raw customer data, ensuring compliance with privacy laws.
References 🔗
- https://en.wikipedia.org/wiki/Privacy-enhancing_technologies
- https://martinfowler.com/articles/intro-pet.html
- https://www.oecd.org/en/publications/emerging-privacy-enhancing-technologies_bf121be4-en.html
- https://theodi.org/insights/projects/privacy-enhancing-technologies-pets/
- https://www.decentriq.com/article/what-are-privacy-enhancing-technologies


